Network Address Translation, commonly known as NAT, is one of the most important technologies in modern computer networking. It acts as a bridge between private local networks and the global internet, making it possible for multiple devices to communicate externally while sharing a single public identity. Without NAT, the structure of the internet as we know it today would not be sustainable, especially given the massive number of devices that are connected every second.
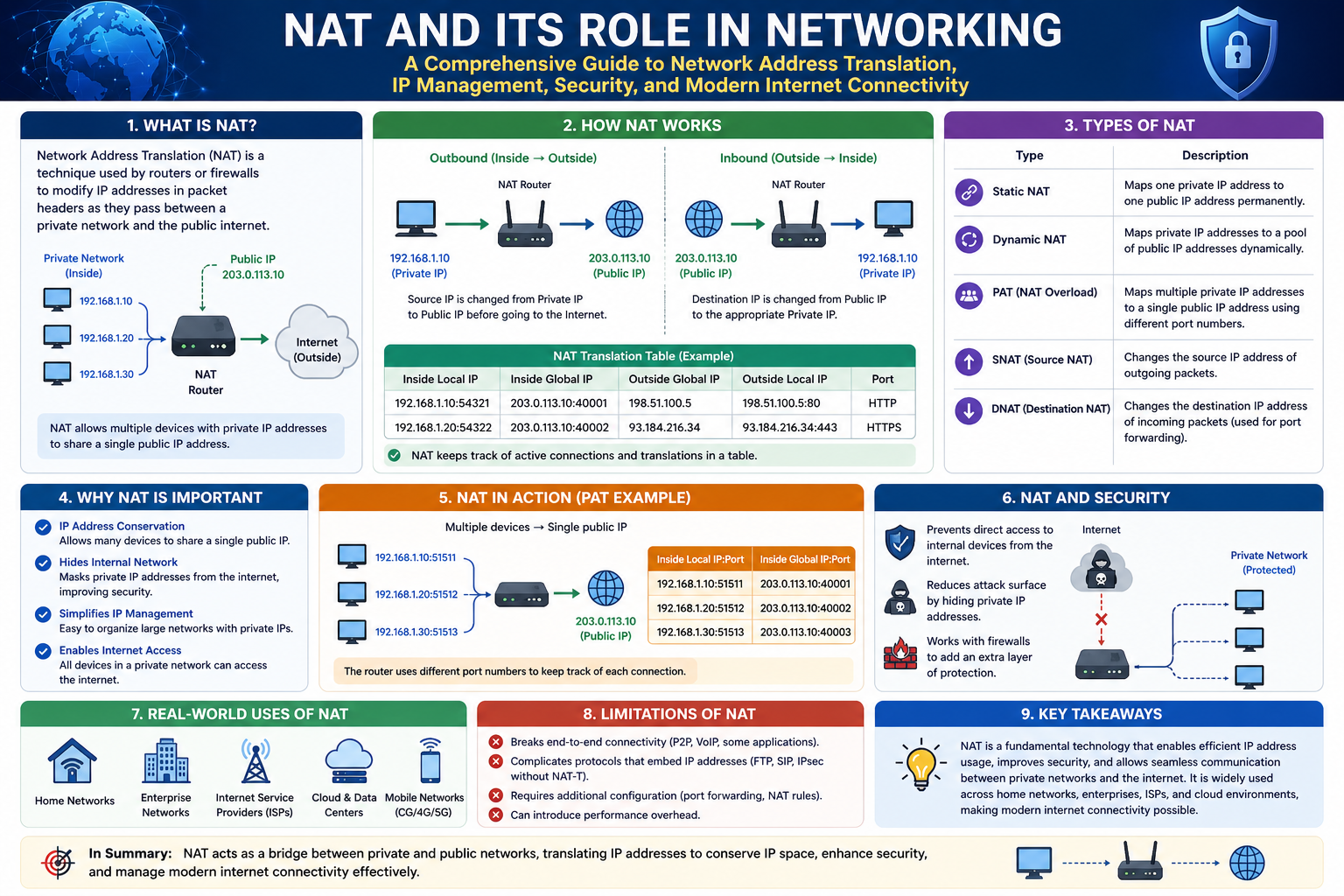
At a basic level, NAT allows devices within a local area network to access the internet using a shared public IP address. This means that instead of every device needing its own globally unique IP, a router can represent all devices behind it. This simple idea has enormous implications, both in terms of efficiency and practicality.
To fully understand NAT, it is important to first explore how IP addressing works and why NAT became necessary in the first place.
The Need for NAT in Modern Networks
The internet relies on IP addresses to identify devices and route data correctly. Every device connected to a network must have an IP address to send and receive information. In the early days of the internet, it was assumed that the number of connected devices would remain relatively small. However, as technology advanced and the internet became widespread, the number of devices quickly exceeded expectations.
IPv4, the most widely used version of the Internet Protocol, provides a limited number of unique IP addresses. While the total number might seem large at first glance, it is not nearly enough to accommodate billions of devices worldwide. This limitation created a significant challenge: how to allow more devices to connect without running out of addresses.
NAT emerged as a practical solution to this problem. By allowing multiple devices to share a single public IP address, NAT significantly reduces the number of public IPs required. Instead of assigning a unique public address to every device, only the router needs one, and it manages communication for all connected devices.
This approach not only conserves IP addresses but also simplifies network management. Organizations and households can operate entire networks without needing a large pool of public IPs, making connectivity more accessible and cost-effective.
Public and Private IP Addresses
To understand how NAT works, it is essential to distinguish between public and private IP addresses. These two types of addresses serve different purposes and operate in different scopes.
Public IP addresses are globally unique and are used to identify devices on the internet. These addresses are assigned by internet service providers and are visible to external networks. When a device communicates with a server on the internet, the public IP address is what the server sees.
Private IP addresses, on the other hand, are used within local networks. These addresses are not accessible from the internet and are reserved for internal use. Common private IP ranges include addresses that begin with 192.168, 10, or 172.16. These ranges are reused across different networks, meaning the same private IP can exist in multiple locations without conflict.
In a typical home network, the router assigns private IP addresses to all connected devices. These devices use their private IPs to communicate with each other and send requests to the router. The router then uses its public IP address to communicate with the internet on behalf of those devices.
This separation between public and private addressing is what makes NAT possible. It allows internal devices to remain hidden from the outside world while still being able to access external resources.
How NAT Works in Practice
NAT operates by modifying network address information as data passes through a router. When a device inside a network sends a request to the internet, the router intercepts the request and alters its source information before forwarding it.
The process begins when a device, such as a laptop or smartphone, attempts to access a website. The device generates a data packet that includes its private IP address and a source port number. This packet is sent to the router, which performs the NAT function.
The router replaces the private IP address with its own public IP address. It also assigns a unique port number to the connection and stores this mapping in a table. This table keeps track of which internal device initiated each connection.
When the request reaches the destination server, it appears to come from the router’s public IP address rather than the original device. The server processes the request and sends a response back to the router.
Upon receiving the response, the router consults its NAT table to determine which internal device should receive the data. It then translates the public IP and port back to the corresponding private IP and original port, delivering the response to the correct device.
This entire process happens almost instantly and continuously for every active connection. Modern routers are capable of handling thousands of such translations simultaneously, ensuring smooth communication for all connected devices.
The Role of Ports in NAT
Ports play a critical role in the NAT process. They act as identifiers that allow multiple connections to be distinguished even when they share the same IP address.
Each outgoing request from a device uses a specific source port. The router may modify this port when performing NAT to ensure that each connection remains unique. This technique is often referred to as Port Address Translation, which is a common form of NAT.
By using ports, the router can manage multiple simultaneous connections from different devices. For example, one device might be browsing the web while another is streaming video and a third is playing an online game. Each of these activities uses different ports, allowing the router to keep track of them independently.
When responses come back from the internet, the router uses the port information to determine where to send the data. This ensures that each device receives the correct response, even though all traffic appears to originate from a single public IP address.
Advantages of NAT
NAT offers several important advantages that make it a fundamental component of modern networking.
One of the most significant benefits is IP address conservation. By allowing multiple devices to share a single public IP, NAT reduces the demand for globally unique addresses. This has helped extend the lifespan of IPv4 and delay the need for a complete transition to newer protocols.
Another advantage is improved security. Since internal devices use private IP addresses, they are not directly accessible from the internet. External systems cannot initiate connections to these devices unless specific configurations are in place. This creates a natural barrier that protects internal networks from unauthorized access.
NAT also simplifies network design and management. Organizations can use consistent private IP ranges without worrying about conflicts with external networks. This makes it easier to set up and maintain internal systems.
Additionally, NAT allows for flexibility in network configuration. Devices can be added or removed without affecting the public-facing structure of the network. The router handles all necessary translations, making changes seamless.
Limitations and Challenges of NAT
Despite its many advantages, NAT is not without its challenges. One of the primary limitations is that it can complicate certain types of communication.
Because NAT modifies address information, it can interfere with protocols that rely on end-to-end connectivity. Some applications, particularly those involving peer-to-peer communication, may struggle to establish direct connections. This is why additional techniques, such as port forwarding, are often required.
NAT can also introduce latency, although this is usually minimal with modern hardware. The process of translating addresses and maintaining connection tables requires processing power, which can affect performance in high-traffic environments.
Another challenge is that NAT breaks the original design principle of the internet, which was based on direct communication between devices. By introducing an intermediary, NAT changes how connections are established and maintained.
In some cases, troubleshooting network issues can become more complex due to NAT. Identifying the source of a problem may require examining both internal and external address mappings, which can be difficult without proper tools.
NAT in Everyday Use
NAT is used in almost every networked environment today. In homes, routers provided by internet service providers typically have NAT enabled by default. This allows multiple devices, such as smartphones, computers, and smart home devices, to share a single internet connection.
In businesses, NAT is used to manage large networks with many devices. It helps organizations maintain efficient communication while controlling access to internal systems.
NAT is also widely used in cloud environments and data centers. It enables scalable architectures where multiple virtual machines can operate behind a limited number of public IP addresses.
Even though users may not always be aware of it, NAT is constantly working in the background, ensuring that data flows smoothly between devices and the internet.
Preparing to Understand NAT Types
While the basic concept of NAT is straightforward, its implementation can vary depending on how a network is configured. Different approaches to NAT can affect how easily devices communicate with external systems and how secure those connections are.
These variations are commonly categorized into three main types: Open NAT, Moderate NAT, and Strict NAT. Each type represents a different level of accessibility and control, influencing how data flows between the internal network and the internet.
Understanding these types is especially important for activities like online gaming, remote access, and hosting services, where connection quality and reliability are critical.
In the next part, we will explore these NAT types in detail, examining how each one works, their advantages and disadvantages, and when they should be used.
Introduction to NAT Types
After understanding how Network Address Translation functions and why it is essential, the next step is to explore how different NAT configurations affect connectivity. NAT is not a single fixed behavior; instead, it can be implemented in different ways depending on how a router handles incoming and outgoing traffic. These variations are commonly grouped into three main categories: Open NAT, Moderate NAT, and Strict NAT.
Each NAT type represents a different level of accessibility between devices inside a private network and systems on the internet. The differences lie in how connections are initiated, how traffic is allowed or restricted, and how the router handles incoming data. These distinctions are especially important in scenarios where real-time communication is required, such as online gaming, voice chat, and peer-to-peer applications.
Understanding these NAT types helps in choosing the right configuration for performance, security, and reliability. It also explains why some connections work seamlessly while others experience delays or restrictions.
What is Open NAT
Open NAT is the least restrictive type of NAT configuration. In this setup, a device inside the network has the highest level of accessibility to the internet. It can freely send and receive data without significant interference from the router. This creates a near-direct communication path between the device and external systems.
In an Open NAT configuration, incoming connections from the internet are allowed to reach the device without being blocked. This means that external servers or peers can initiate communication without needing a pre-existing request from the internal device. As a result, applications that rely on direct connections perform more efficiently.
One way Open NAT is achieved is through port forwarding. In this method, specific ports on the router are assigned to a particular device within the network. Any incoming traffic on those ports is automatically directed to that device. This eliminates the need for the router to dynamically translate connections for those ports, reducing delays and improving responsiveness.
Another approach sometimes used is placing a device in a demilitarized zone, commonly referred to as a DMZ. In this configuration, the device is exposed directly to the internet with minimal filtering. While this provides maximum connectivity, it also removes many of the protective features of the router.
Open NAT is particularly beneficial for applications that require consistent and fast communication. Online gaming is one of the most common examples. Many multiplayer games rely on direct peer-to-peer connections or require incoming traffic from game servers. With Open NAT, these connections are established quickly and reliably.
However, this level of openness comes with trade-offs. Because the router allows incoming traffic more freely, the device is more exposed to potential threats. Without proper safeguards, it may be vulnerable to unauthorized access or malicious activity. For this reason, Open NAT should be used carefully and only when necessary.
How Open NAT Affects Performance
Open NAT typically provides the best performance among the three NAT types. Since there are fewer restrictions on incoming and outgoing traffic, data can flow more efficiently between the device and the internet. This is especially important for applications that require low latency and real-time interaction.
In gaming, for example, Open NAT reduces the chances of lag, disconnections, and matchmaking issues. Players can connect to a wider range of peers and servers, resulting in a smoother experience. Voice communication and video streaming also benefit from the reduced delays.
The absence of strict filtering means that packets are less likely to be dropped or delayed. The router does not need to perform complex checks for each incoming connection, which speeds up the overall communication process.
Despite these advantages, performance improvements must be weighed against security considerations. While Open NAT can enhance speed and reliability, it also reduces the protective role of the router.
What is Moderate NAT
Moderate NAT represents a balanced approach between accessibility and security. It is the most common NAT configuration found in home and office networks. In this setup, devices can freely initiate connections to the internet, but incoming connections are more controlled.
With Moderate NAT, outbound traffic works normally. When a device sends a request, the router translates the address and allows the response to return. However, external systems cannot initiate connections to the device unless a corresponding outbound request already exists.
This behavior is often referred to as stateful communication. The router keeps track of active connections and only allows incoming traffic that matches an existing session. Any unsolicited incoming traffic is blocked by default.
Moderate NAT provides a good level of protection while still supporting most online activities. Web browsing, streaming, and many online games function well under this configuration. Since the router handles translations dynamically, there is no need for manual configuration in most cases.
For gaming, Moderate NAT allows connections to players with Open NAT and other Moderate NAT users. However, it may have difficulty connecting with devices that are behind Strict NAT. This can sometimes result in limited matchmaking options or longer connection times.
Benefits of Moderate NAT
Moderate NAT offers a practical balance between usability and security. It allows users to access most online services without needing complex configurations while still maintaining a level of protection against unwanted traffic.
One of the key advantages is ease of use. Most routers are configured with Moderate NAT by default, meaning users do not need to adjust settings to get started. This makes it ideal for general-purpose networking.
Security is another important benefit. Since the router blocks unsolicited incoming connections, internal devices are shielded from many types of external threats. This reduces the risk of unauthorized access and helps maintain network integrity.
Moderate NAT also supports a wide range of applications. While it may not provide the same level of openness as Open NAT, it is sufficient for most everyday tasks, including streaming, browsing, and many forms of online communication.
Limitations of Moderate NAT
Although Moderate NAT is versatile, it is not without limitations. One of the main challenges is that it can restrict certain types of connections. Applications that require direct inbound communication may not function optimally without additional configuration.
In gaming, this can lead to issues such as difficulty joining certain sessions or hosting games. Players may experience longer wait times when connecting to others, especially if multiple participants are using restrictive NAT types.
Some peer-to-peer applications may also encounter connectivity issues. Since the router blocks unsolicited incoming traffic, establishing direct connections between devices can be more complex.
Despite these limitations, Moderate NAT remains the preferred choice for most users due to its balance of convenience and security.
Comparing Open NAT and Moderate NAT
The primary difference between Open NAT and Moderate NAT lies in how incoming connections are handled. Open NAT allows incoming traffic more freely, enabling direct communication between devices. Moderate NAT, on the other hand, restricts incoming traffic to responses associated with existing connections.
This difference affects both performance and security. Open NAT provides better connectivity and lower latency but exposes devices to greater risk. Moderate NAT offers improved security by limiting access while still supporting most online activities.
Choosing between the two depends on the specific requirements of the user. For general use, Moderate NAT is usually sufficient. For applications that demand high performance and direct connectivity, Open NAT may be more suitable, provided that appropriate security measures are in place.
Real-World Use Cases for Open and Moderate NAT
Open NAT is commonly used in scenarios where performance and connectivity are critical. Online gaming is the most prominent example, as it often requires fast and reliable communication between players. Hosting servers or running applications that need inbound connections also benefits from Open NAT.
Moderate NAT is ideal for everyday use. It supports common activities such as browsing the web, streaming media, and using online services without requiring manual configuration. It is also suitable for environments where security is a concern but strict restrictions are not necessary.
In many cases, users may start with Moderate NAT and switch to Open NAT only when needed. This approach allows them to maintain a secure environment while still having the option to optimize performance for specific applications.
Preparing for Strict NAT
While Open and Moderate NAT cover a wide range of use cases, there are situations where tighter control is required. This is where Strict NAT comes into play. It introduces additional restrictions on communication, focusing on limiting access to specific ports and connections.
Strict NAT is typically used in environments where security is a top priority. It ensures that only explicitly allowed traffic can pass through the network, reducing the risk of unauthorized access.
In the next part, we will explore Strict NAT in detail, examining how it works, its advantages, and when it should be used.
Introduction to Strict NAT
After exploring Open NAT and Moderate NAT, the final type to understand is Strict NAT. This configuration represents the most restrictive approach to handling network traffic. While the previous NAT types aim to balance accessibility and performance, Strict NAT prioritizes control and security above all else.
Strict NAT is designed to limit how devices communicate with external networks. It enforces tight rules on both incoming and outgoing traffic, ensuring that only explicitly allowed connections are permitted. This makes it particularly useful in environments where protecting data and preventing unauthorized access are top priorities.
Although Strict NAT can reduce flexibility and make certain applications more difficult to use, it plays an important role in securing sensitive networks. Understanding how it works helps in determining when such restrictions are necessary and how they impact overall connectivity.
What is Strict NAT
Strict NAT is a configuration in which the router tightly controls which connections are allowed to pass between the internal network and the internet. Unlike Open NAT, which allows broad access, and Moderate NAT, which allows controlled responses, Strict NAT limits communication to very specific conditions.
In this setup, devices inside the network can still initiate outbound connections, but the router enforces strict rules on how these connections are handled. Only predefined ports and protocols may be allowed, and incoming traffic is heavily filtered. If a connection does not meet the configured criteria, it is blocked.
One of the defining characteristics of Strict NAT is that it often requires manual configuration. Network administrators specify which ports are open and which services are permitted. This creates a controlled environment where only known and trusted communication is allowed.
Because of these restrictions, devices behind Strict NAT have limited ability to accept incoming connections. External systems cannot freely initiate communication, and even responses may be subject to additional checks before being allowed through.
How Strict NAT Handles Traffic
Strict NAT operates by applying strict filtering rules to network traffic. When a device sends a request to the internet, the router examines the request and determines whether it meets the allowed criteria. If it does, the request is translated and forwarded.
When a response is received, the router again checks whether the incoming data matches an approved connection. In many cases, additional validation is required beyond simply matching an existing session. This ensures that only legitimate and expected traffic is allowed.
The router may also restrict which ports can be used for communication. For example, it might allow only web traffic over specific ports while blocking all other types of connections. This reduces the attack surface by limiting the number of entry points available to external systems.
In some implementations, Strict NAT can involve static rules that define exactly how traffic should be handled. These rules may include access control lists or firewall policies that specify which connections are permitted and which are denied.
This level of control makes Strict NAT highly effective for securing networks, but it also introduces complexity and potential limitations.
Security Benefits of Strict NAT
The primary advantage of Strict NAT is its strong focus on security. By limiting communication to only approved connections, it significantly reduces the risk of unauthorized access. External systems cannot easily reach devices within the network, making it more difficult for attackers to exploit vulnerabilities.This controlled approach ensures that all incoming and outgoing traffic is carefully filtered and validated. Only connections that meet predefined rules are allowed, which helps prevent unexpected or suspicious activity from entering the network. As a result, Strict NAT acts as a strong barrier against common threats such as unauthorized login attempts, port scanning, and certain types of malware communication.
Another important aspect of Strict NAT is its ability to enforce strict port-level control. By allowing only specific ports to be used, it limits the number of possible entry points into the network. This significantly reduces the attack surface, making it harder for attackers to identify and exploit weaknesses. Even if a vulnerability exists, the chances of it being reached are minimized due to these restrictions.
Strict NAT also enhances internal security by regulating outbound traffic. If a device within the network becomes compromised, its ability to communicate with external malicious servers can be restricted. This helps contain potential threats and prevents data from being transmitted without authorization. In this way, Strict NAT not only protects against external attacks but also helps mitigate internal risks.
Additionally, this configuration improves monitoring and control. Since all allowed traffic is intentional and predefined, it becomes easier for administrators to track network activity and identify unusual patterns. This visibility supports quicker detection of potential issues and strengthens overall network management.
Overall, Strict NAT creates a highly controlled environment where security is prioritized, making it a reliable choice for networks that require strong protection and strict access management.
Strict NAT also helps prevent unwanted outbound traffic. By controlling which ports and protocols can be used, it can block malicious software from communicating with external servers. This is particularly useful in environments where data protection is critical.
Another benefit is improved visibility and control. Since all allowed connections must be defined, administrators have a clear understanding of network activity. This makes it easier to monitor traffic and identify unusual behavior.
In high-security environments, such as corporate networks or systems handling sensitive information, these benefits are essential. Strict NAT provides a controlled framework that supports strong security policies.
Limitations of Strict NAT
While Strict NAT offers enhanced security, it also comes with significant limitations. One of the most notable challenges is reduced connectivity. Many applications rely on the ability to establish direct or flexible connections, which can be restricted under Strict NAT.
In online gaming, for example, Strict NAT can lead to difficulties in connecting with other players. Matchmaking may take longer, and certain multiplayer features may not work as intended. This is because the restrictive nature of Strict NAT prevents the necessary communication from being established.
Voice and video communication applications may also be affected. These services often require real-time data exchange and may struggle to function properly when connections are heavily filtered.
Another limitation is the need for manual configuration. Setting up Strict NAT requires defining rules for allowed traffic, which can be complex and time-consuming. Incorrect configurations can lead to connectivity issues or unintended restrictions.
Additionally, troubleshooting problems in a Strict NAT environment can be more difficult. Since many connections are blocked by default, identifying the cause of an issue may require detailed analysis of network rules and logs.
Comparing Strict NAT with Other NAT Types
Strict NAT differs significantly from Open NAT and Moderate NAT in how it manages traffic. Open NAT allows the most freedom, enabling direct communication with minimal restrictions. Moderate NAT provides a balance by allowing outgoing connections and controlled responses.
Strict NAT, in contrast, focuses on limiting access as much as possible. It enforces strict rules that govern how and when communication can occur. This results in a more secure but less flexible environment.
From a performance perspective, Strict NAT may introduce delays or prevent certain connections altogether. While it does not necessarily slow down approved traffic, the restrictions can impact overall usability.
From a security standpoint, Strict NAT provides the highest level of protection among the three types. It minimizes exposure to external threats and ensures that only authorized communication takes place.
Choosing between these NAT types involves considering the trade-offs between security and accessibility. Each type serves a different purpose and is suited to different scenarios.
When to Use Strict NAT
Strict NAT is most appropriate in environments where security is a top priority. This includes corporate networks, government systems, and any setup where sensitive data must be protected from unauthorized access.
It is also useful in situations where specific services need to be tightly controlled. For example, a network may allow only web browsing while blocking all other types of traffic. This ensures that users can perform necessary tasks without exposing the network to unnecessary risks.
In some cases, Strict NAT may be used temporarily to investigate or contain security issues. By restricting communication, administrators can prevent potential threats from spreading or communicating with external systems.
However, Strict NAT is generally not recommended for everyday home use unless there is a specific need for heightened security. The limitations it introduces can outweigh its benefits in typical scenarios.
Balancing Security and Usability
One of the key challenges in networking is finding the right balance between security and usability. While Strict NAT provides strong protection, it can make certain applications difficult or impossible to use. On the other hand, more open configurations improve accessibility but increase exposure to risks.This balance becomes especially important in real-world environments where users expect both safety and seamless performance. For example, in a home network, users may prioritize smooth streaming, gaming, and video calls, which often benefit from fewer restrictions. In such cases, a more open or moderate configuration can provide a better experience without significantly compromising safety if other protections are in place.
In contrast, business or enterprise networks typically place a higher emphasis on security. Sensitive data, internal systems, and user access must be carefully controlled, making stricter configurations more appropriate. However, even in these environments, excessive restrictions can reduce productivity by limiting access to necessary tools and services.
Achieving the right balance often involves combining NAT settings with additional security layers such as firewalls, intrusion detection systems, and proper network policies. Instead of relying solely on one approach, administrators can tailor configurations to meet specific needs, ensuring both protection and functionality are maintained.
The choice of NAT type should be based on the specific requirements of the network. For general use, Moderate NAT often provides the best balance. For performance-critical applications, Open NAT may be preferred. For secure environments, Strict NAT is the most suitable option.
In many cases, networks may use a combination of approaches. Certain devices or services may be configured with more open settings, while others remain restricted. This allows for flexibility while maintaining overall security.
Understanding how each NAT type functions makes it easier to design a network that meets both performance and security needs.
Conclusion
Network Address Translation remains one of the most practical and widely used solutions in modern networking. Across all three NAT types—Open NAT, Moderate NAT, and Strict NAT—it becomes clear that each configuration is designed with a specific purpose in mind. Rather than one type being universally better than the others, each serves a different balance of performance, accessibility, and security.
Strict NAT, as discussed in this part, stands out for its emphasis on control and protection. By allowing only predefined and carefully managed connections, it creates a tightly secured environment where the risk of unauthorized access is significantly reduced. This makes it especially valuable in scenarios where data sensitivity and network integrity are critical. Organizations that handle confidential information, financial systems, or internal infrastructure often rely on stricter configurations to ensure that only approved traffic is allowed.
However, this level of control introduces trade-offs that cannot be ignored. Strict NAT can limit connectivity, disrupt certain applications, and require more effort to configure and maintain. Activities that depend on real-time communication or peer-to-peer interaction may not function as smoothly, which can impact user experience. This highlights an important reality in networking: stronger security often comes at the cost of convenience and flexibility.
When comparing all NAT types together, a clear spectrum emerges. Open NAT provides maximum accessibility and performance, allowing devices to communicate freely with minimal restrictions. Moderate NAT offers a balanced approach, supporting most applications while maintaining a reasonable level of protection. Strict NAT, on the other hand, prioritizes security by enforcing tight controls over network traffic.
Choosing the right NAT type depends entirely on the needs of the network. For everyday use, Moderate NAT is typically the most practical option, as it delivers reliable performance without requiring complex setup. For specialized use cases such as online gaming or hosting services, Open NAT may be necessary to ensure smooth connectivity. In contrast, Strict NAT is best suited for environments where security requirements outweigh the need for flexibility.
It is also important to recognize that NAT is not a complete security solution on its own. While it provides a layer of protection by limiting direct access to internal devices, it should be combined with other measures such as firewalls, encryption, and regular system updates. A well-designed network uses multiple layers of defense to achieve both safety and efficiency.
Ultimately, understanding NAT types empowers users and administrators to make informed decisions about their network configurations. By selecting the appropriate level of openness or restriction, it is possible to create a system that meets both performance expectations and security requirements. As networks continue to evolve and the number of connected devices grows, the role of NAT will remain essential in maintaining efficient and secure communication across the internet.