When people browse the internet, the experience feels almost effortless. A user types a website address into a browser, presses enter, and within moments a fully rendered webpage appears. Behind this simplicity lies a structured system of communication that relies on protocols, ports, and layers working together seamlessly. One of the most essential components in this system is port 80, which has historically served as the default gateway
for web traffic.
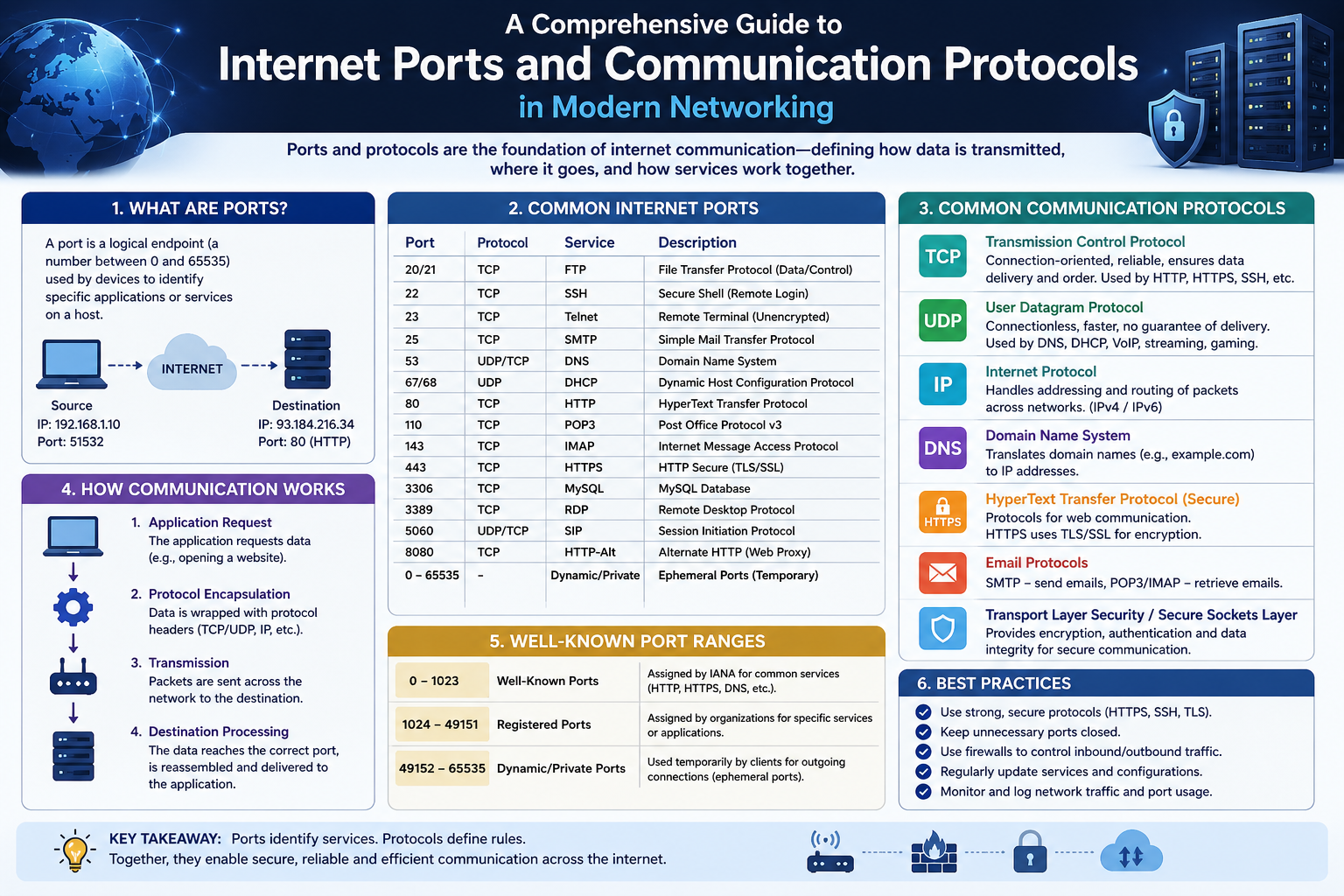
In networking, a port is a logical endpoint used by computers to manage different types of communication. Each port is assigned a number and associated with specific services or protocols. This allows a single device to handle multiple types of network traffic simultaneously without confusion. For example, one port may handle email, another file transfers, and another web browsing.
Port 80 is specifically associated with HTTP, the HyperText Transfer Protocol. This protocol governs how web data is requested and delivered between a client, such as a browser, and a server. Understanding port 80 is essential for anyone looking to build a strong foundation in networking, web development, or cybersecurity.
What Is Port 80
Port 80 is the default port used for HTTP communication. Whenever a user accesses a website that begins with http rather than https, the browser sends its request through port 80. This port acts as a channel through which data flows between the user’s device and the web server hosting the requested content.
Ports can be thought of as doors on a computer. Each door is assigned a number and is used for a specific purpose. Port 80 is the door designated for HTTP traffic. When a browser wants to retrieve a webpage, it knocks on this door to request the necessary data.
This process happens automatically without the user needing to specify the port number. For example, when someone types a website address into a browser without including a port, the browser assumes port 80 for HTTP communication. This default behavior simplifies the user experience and standardizes how web traffic is handled.
The Role of HTTP in Web Browsing
HTTP is the protocol that defines how messages are formatted and transmitted across the web. It operates on a request and response model. The client sends a request to the server, and the server responds with the requested data.
When a user visits a website, the browser sends an HTTP request that includes details such as the type of request and the resource being requested. The most common type of request is a GET request, which asks the server to provide a specific resource, such as a web page.
Once the server receives the request, it processes it and sends back a response. This response typically includes HTML content, along with other resources like CSS and JavaScript files. The browser then interprets this data and renders the webpage for the user.
HTTP operates at the application layer of networking. This layer is responsible for providing services directly to users and applications. While HTTP handles the structure of communication, it relies on lower-level protocols to ensure that data is transmitted correctly.
How Port 80 Facilitates Data Exchange
Port 80 serves as the pathway through which HTTP messages travel. Without this port, there would be no standardized way for browsers and servers to communicate using HTTP. It acts as a central hub for web traffic, enabling consistent and predictable data exchange.
When a browser initiates a connection, it sends a request to the server’s IP address on port 80. The server listens on this port for incoming requests and responds accordingly. This interaction happens millions of times every second across the internet.
The data exchanged through port 80 is typically broken into smaller units called packets. These packets are transmitted across networks and reassembled at their destination. This process ensures efficient and reliable communication, even over long distances.
TCP and the Reliability of Port 80
Port 80 uses TCP, or Transmission Control Protocol, as its underlying transport mechanism. TCP is designed to provide reliable and ordered delivery of data. It ensures that all packets reach their destination and are reassembled correctly.
Before any data is transmitted, TCP establishes a connection between the client and the server using a process known as the three way handshake. This process involves three steps that confirm both sides are ready to communicate.
First, the client sends a synchronization request to the server. Second, the server acknowledges this request and signals its readiness. Third, the client confirms the acknowledgment, and the connection is established. Only after this handshake is complete does data transmission begin.
This approach ensures that communication is stable and reduces the risk of data loss. If any packets are lost during transmission, TCP detects the issue and retransmits the missing data. This makes port 80 highly reliable for delivering web content.
The Simplicity and Advantages of Port 80
One of the main reasons port 80 became widely adopted is its simplicity. HTTP does not require encryption or complex setup, making it easy to implement and use. This simplicity played a major role in the early growth of the internet.
Developers can quickly set up web servers using port 80 without needing to manage certificates or encryption keys. This makes it a convenient option for testing and development environments.
Another advantage is compatibility. Since port 80 has been the standard for HTTP for decades, it is supported by virtually all devices, browsers, and servers. This universal support ensures that web content can be accessed from almost anywhere.
Lack of Encryption and Security Concerns
Despite its advantages, port 80 has a significant drawback: it does not provide encryption. Data transmitted through this port is sent in plain text, meaning it can be read by anyone who intercepts it.
This lack of security makes communication over port 80 highly vulnerable to various cyber threats, including eavesdropping, data theft, and man-in-the-middle attacks. Attackers can capture sensitive information such as login credentials, personal details, and session cookies without needing advanced tools, especially when users are connected to unsecured or public networks.
In addition, because the data is not encrypted, it can also be modified in transit. This means an attacker could inject malicious code into a webpage, redirect users to fake websites, or alter the content being delivered without the user’s knowledge. Such risks can lead to serious consequences, including identity theft, financial loss, and compromised systems. As a result, modern web standards strongly discourage the use of port 80 for transmitting sensitive information.
To address these concerns, most websites now use HTTPS, which operates over port 443 and provides encryption through SSL/TLS protocols. This ensures that data remains confidential and secure during transmission. While port 80 is still used for basic or non-sensitive communication and for redirecting users to secure connections, relying solely on it in today’s security-conscious environment is no longer considered a safe practice.
This lack of security poses several risks. Sensitive information such as login credentials, personal data, and financial details can be exposed if transmitted over HTTP. Attackers can use tools to capture and analyze this data.
Another concern is data integrity. Because HTTP does not include mechanisms to verify the authenticity of data, attackers can modify the content during transmission. This can lead to the injection of malicious scripts or altered information.
It is important to understand that the port itself is not inherently insecure. The issue lies with the HTTP protocol, which does not include encryption by default. As a result, communication over port 80 is vulnerable to various types of attacks.
Common Uses of Port 80 in Modern Networks
Although port 80 is no longer considered secure for public communication, it still has practical uses. One of the most common uses is redirection. When a user attempts to access a website using HTTP, the server often redirects the request to a secure HTTPS version.
This automatic redirection ensures that users are quickly moved to a safer, encrypted connection without needing to manually change the URL. It also helps maintain compatibility with older links, bookmarks, or systems that still rely on HTTP by seamlessly guiding traffic to the secure version of a website.
Another important use of port 80 is for initial connectivity and testing purposes within controlled environments. Network administrators and developers often use it for troubleshooting web services, verifying server responses, or testing configurations before deploying secure connections. In internal networks where security risks are limited, port 80 can still be used for non-sensitive data transfer and basic web services.
Additionally, port 80 plays a role in handling web crawlers and search engine indexing. Some bots initially connect over HTTP before being redirected, allowing websites to manage traffic efficiently. It is also commonly used in load balancers and reverse proxies to receive incoming requests before forwarding them to secure back-end servers. Overall, while port 80 is no longer ideal for secure communication, it remains a useful component in modern web infrastructure when used appropriately.
This redirection helps ensure that users ultimately communicate over a secure channel. It also allows websites to maintain compatibility with older links and bookmarks that use HTTP.
Port 80 is also used in internal networks where security risks are lower. For example, organizations may use HTTP for communication between internal systems that are protected by firewalls and other security measures.
Developers frequently use port 80 for testing applications. Since it does not require encryption, it simplifies the development process and allows for faster troubleshooting.
Port 80 and Load Balancing
In large scale systems, port 80 is often used in conjunction with load balancers. A load balancer distributes incoming traffic across multiple servers to ensure optimal performance and reliability.
When traffic arrives on port 80, the load balancer determines which server should handle the request. This helps prevent any single server from becoming overwhelmed.
In some cases, the load balancer may handle encryption separately, allowing backend servers to communicate using HTTP. This approach reduces the computational overhead on individual servers while maintaining overall security.
The Decline of Port 80 for Public Websites
As cybersecurity threats have increased, the use of port 80 for public websites has declined. Modern users expect secure communication, and organizations are under pressure to protect user data.
Web browsers now display warnings when users visit sites that use HTTP instead of HTTPS. These warnings can discourage users from continuing, leading to a loss of traffic and trust.
Search engines also prioritize secure websites in their rankings. Sites that rely solely on HTTP may appear lower in search results, reducing their visibility.
Because of these factors, most websites have transitioned to using secure protocols. Port 80 is often used only as a fallback or for redirection purposes.
Understanding Port 80 in the Context of Networking Layers
Port 80 operates within a layered networking model. HTTP functions at the application layer, which is responsible for user interactions. Below this layer are transport, network, and physical layers that handle data transmission.
TCP operates at the transport layer, ensuring reliable delivery of data. The network layer handles routing, while the physical layer deals with the actual transmission of signals.
Each layer has a specific role, and together they create a complete communication system. Port 80 is an essential part of this system, enabling HTTP to function effectively.
Why Learning Port 80 Still Matters
Even though secure communication has become the standard, understanding port 80 remains important. It provides insight into how the web evolved and how modern systems are built.
Many networking concepts are easier to understand when starting with HTTP and port 80. These concepts form the foundation for more advanced topics, including secure communication and encryption.
For students preparing for certifications or careers in IT, a solid understanding of port 80 is essential. It helps build the knowledge needed to work with web servers, troubleshoot network issues, and design secure systems.
Introduction to Secure Internet Communication
As the internet evolved, the need for secure communication became increasingly important. Early web traffic relied heavily on HTTP and port 80, which allowed data to travel freely between clients and servers. While this approach was simple and efficient, it lacked one critical element: security. Over time, cyber threats grew more sophisticated, and the risks associated with unencrypted communication became impossible to ignore.
This shift led to the widespread adoption of HTTPS, a secure version of HTTP that operates on port 443. HTTPS introduced encryption, authentication, and data integrity, transforming how information is transmitted across the web. Today, it is the standard for secure browsing and is used by nearly all modern websites.
Understanding port 443 and HTTPS is essential for grasping how secure communication works. It builds upon the concepts introduced with port 80 but adds layers of protection that safeguard data from interception and tampering.
What Is Port 443
Port 443 is the default port used for HTTPS communication. Just as port 80 is associated with HTTP, port 443 is reserved for secure web traffic. When a user accesses a website that begins with https, the browser automatically connects to the server through port 443.
This port acts as a secure gateway for data transmission. It ensures that communication between the client and server is encrypted, making it significantly more difficult for unauthorized parties to access or manipulate the data.
Like all ports, port 443 is not inherently secure on its own. Its security comes from the protocols that operate on it, specifically TLS. Together, port 443 and TLS create a secure channel for web communication.
What Is HTTPS
HTTPS stands for HyperText Transfer Protocol Secure. It is essentially an enhanced version of HTTP that includes encryption and security features. While HTTP focuses on how data is structured and transmitted, HTTPS adds mechanisms to protect that data.
When a user visits a website using HTTPS, the browser and server establish a secure connection before any data is exchanged. This connection ensures that all information transmitted during the session is encrypted and protected from eavesdropping.
HTTPS is used for a wide range of applications, including online banking, e commerce, email, and social media. Any situation that involves sensitive data benefits from the security provided by HTTPS.
The Meaning of Encryption in HTTPS
Encryption is the process of converting readable data into an unreadable format. This ensures that even if data is intercepted, it cannot be understood without the appropriate key.
In the context of HTTPS, encryption protects data as it travels between the client and server. This includes everything from login credentials to personal information and financial transactions.
When a user sends a request to a secure website, the data is encrypted before it leaves the device. It remains encrypted during transmission and is only decrypted when it reaches the intended server. The server then processes the request and sends an encrypted response back to the client.
This process ensures confidentiality, meaning that only authorized parties can access the information.
The Role of TLS in Secure Communication
TLS, or Transport Layer Security, is the protocol responsible for encryption in HTTPS. It operates between the application layer and the transport layer, adding a layer of security to standard communication.
TLS evolved from an older protocol known as SSL, which is now considered obsolete. Modern systems rely exclusively on TLS for secure communication.
When a connection is established over port 443, TLS initiates a handshake process. This process allows the client and server to agree on encryption methods and exchange keys securely.
The TLS handshake involves several steps, including verifying the server’s identity and generating encryption keys. Once the handshake is complete, all subsequent communication is encrypted.
The TLS Handshake Process
The TLS handshake is a critical component of secure communication. It ensures that both the client and server can trust each other and establish a secure session.
The process begins when the client sends a request to the server, indicating that it wants to establish a secure connection. The server responds by providing its digital certificate, which contains its public key.
The client verifies the certificate to ensure that it is valid and issued by a trusted authority. Once the certificate is verified, the client generates a session key and encrypts it using the server’s public key. This encrypted key is sent to the server.
The server uses its private key to decrypt the session key. From this point forward, both the client and server use the session key to encrypt and decrypt data during the session.
This process combines asymmetric and symmetric encryption, providing both security and efficiency.
Asymmetric and Symmetric Encryption
HTTPS relies on two types of encryption: asymmetric and symmetric. Each plays a specific role in securing communication.
Asymmetric encryption uses a pair of keys: a public key and a private key. The public key is shared openly, while the private key is kept secret. Data encrypted with the public key can only be decrypted with the private key.
This method is used during the initial stages of the TLS handshake to securely exchange the session key.
Symmetric encryption, on the other hand, uses a single key for both encryption and decryption. Once the session key is established, symmetric encryption is used for the rest of the communication.
This approach is more efficient and allows for faster data transmission while maintaining security.
Digital Certificates and Authentication
Digital certificates play a crucial role in HTTPS. They are used to verify the identity of a website and establish trust between the client and server.
A certificate is issued by a trusted organization known as a certificate authority. It contains information about the website, including its domain name and public key.
When a user connects to a secure website, the browser checks the certificate to ensure it is valid. If the certificate is expired, invalid, or issued by an untrusted authority, the browser may display a warning.
This verification process helps prevent attacks where malicious actors impersonate legitimate websites.
The Importance of Data Integrity
In addition to encryption and authentication, HTTPS ensures data integrity. This means that the data cannot be altered during transmission without detection.
TLS uses cryptographic techniques to generate a message authentication code for each piece of data. When the data is received, the recipient verifies the code to ensure it has not been modified.
If any changes are detected, the data is rejected, and the connection may be terminated. This protects users from tampered content and malicious interference.
Why Port 443 Is the Standard for HTTPS
Port 443 has become the standard for HTTPS because it provides a consistent and widely recognized endpoint for secure communication. Using a standard port simplifies network configuration and ensures compatibility across systems.
Firewalls and security systems are typically configured to allow traffic on port 443, making it easier for secure connections to pass through. If HTTPS were to use nonstandard ports, it could lead to connectivity issues.
Although HTTPS can technically operate on other ports, using port 443 is the most practical and reliable choice.
Common Uses of HTTPS in Modern Applications
HTTPS is used in nearly every aspect of modern internet activity. It is essential for protecting sensitive information and ensuring secure interactions.
Online banking platforms rely on HTTPS to safeguard financial transactions. E commerce websites use it to protect customer data and payment details. Email services use HTTPS to secure communication between users and servers.
Even websites that do not handle sensitive data often use HTTPS to provide a secure browsing experience and build user trust.
Security Benefits of HTTPS
HTTPS offers several important security benefits. It protects data from being intercepted by unauthorized parties. It ensures that users are communicating with legitimate websites. It prevents data from being altered during transmission.
These benefits make HTTPS essential for maintaining privacy and security on the internet. Without it, users would be exposed to a wide range of risks.
Limitations and Vulnerabilities of HTTPS
While HTTPS is highly secure, it is not completely immune to vulnerabilities. Many of these issues arise from misconfiguration or poor maintenance rather than flaws in the protocol itself.
One common issue is expired certificates. If a certificate is not renewed on time, it can lead to warnings and potential security risks. Another issue is improper implementation, which can create opportunities for attackers.
There are also advanced attack techniques, such as man in the middle attacks, where an attacker attempts to intercept communication. However, HTTPS significantly reduces the likelihood and impact of such attacks.
The Role of User Awareness in Security
Even with strong encryption, user behavior plays a critical role in maintaining security. Users must be aware of potential risks and take precautions when browsing the internet.
Checking for HTTPS indicators, such as the padlock icon in the browser, is one way to ensure a secure connection. Avoiding suspicious websites and keeping software up to date also helps reduce risk.
Security is a shared responsibility between technology and users.
The Evolution Toward a Secure Web
The adoption of HTTPS represents a major shift in how the internet operates. What was once optional has now become the standard. Organizations, developers, and users all recognize the importance of secure communication.
Many browsers now enforce HTTPS by default, and search engines prioritize secure websites. This trend reflects a broader commitment to protecting user data and privacy.
As technology continues to evolve, security will remain a central focus. HTTPS and port 443 will continue to play a key role in shaping the future of the internet.
Introduction to the Comparison
After understanding how port 80 supports HTTP and how port 443 enables HTTPS, the next step is to examine how these two ports compare in real-world scenarios. Both are essential to internet communication, and both were designed to facilitate the transfer of web data between clients and servers. However, the way they handle that task differs significantly, especially when it comes to security, reliability, and modern usage.
Although they share a common purpose, the differences between port 80 and port 443 have reshaped how the internet operates today. This comparison is not just theoretical. It has practical implications for developers, businesses, and everyday users who rely on secure and efficient communication.
Core Functional Similarities
At their core, port 80 and port 443 serve the same fundamental purpose: enabling communication between a client and a server. Both ports are used to transmit web content such as HTML pages, images, scripts, and other resources required to display a website.
When a browser sends a request to a server, it uses one of these ports depending on whether the connection is secure or not. The server then responds with the requested data, allowing the browser to render the content.
Both ports rely on structured protocols that define how requests and responses are handled. They also depend on underlying transport mechanisms to ensure data is delivered correctly. In this sense, they are part of the same ecosystem and work in similar ways at a basic level.
Key Differences in Security
The most important difference between port 80 and port 443 is security. Port 80 uses HTTP, which does not include encryption. This means that any data transmitted through port 80 can potentially be intercepted and read by unauthorized parties.
Port 443, on the other hand, uses HTTPS, which incorporates encryption through TLS. This ensures that data is protected during transmission and cannot be easily accessed by attackers.
This distinction has major implications. For example, when a user enters login credentials on a website using HTTP, those credentials are transmitted in plain text. If the same action is performed over HTTPS, the credentials are encrypted and protected.
Security is no longer optional in modern web applications. As a result, port 443 has become the preferred choice for nearly all public facing websites.
Differences in Data Integrity and Authentication
Another major difference lies in how data integrity and authentication are handled. HTTP does not provide built in mechanisms to verify that data has not been altered during transmission. This makes it vulnerable to tampering and injection attacks.
HTTPS addresses this issue by using cryptographic techniques to ensure data integrity. Each piece of data is accompanied by verification information that allows the recipient to confirm it has not been modified.
Authentication is also a key feature of HTTPS. Digital certificates are used to verify the identity of the server, ensuring that users are communicating with the intended website. This helps prevent impersonation and phishing attacks.
Port 80 lacks these protections, making it less suitable for environments where trust and authenticity are important.
Performance Considerations
In the past, one of the arguments in favor of HTTP and port 80 was performance. Since HTTP does not require encryption, it involves less computational overhead. This made it faster in early implementations.
However, advancements in technology have largely eliminated this advantage. Modern hardware and optimized protocols allow HTTPS to perform efficiently, even with encryption.
Techniques such as session reuse and improved encryption algorithms have reduced the performance gap. In many cases, users do not notice any difference in speed between HTTP and HTTPS.
As a result, performance is no longer a valid reason to avoid using port 443.
SEO and User Trust
Search engines and user expectations have also influenced the shift toward HTTPS. Websites that use secure connections are often ranked higher in search results. This gives them greater visibility and increases traffic.
Users are also more likely to trust websites that display security indicators, such as a padlock icon in the browser. These indicators signal that the site is using HTTPS and that data is protected.
Websites that rely on HTTP may be flagged as insecure, which can discourage users from interacting with them. This can lead to reduced engagement and loss of credibility.
Port 443 plays a crucial role in building trust and maintaining a positive user experience.
Redirection from Port 80 to Port 443
One of the most common practices in modern web development is redirecting traffic from port 80 to port 443. When a user attempts to access a website using HTTP, the server automatically redirects the request to the secure HTTPS version.
This ensures that users always interact with the secure version of the site, even if they initially use an insecure link. It also helps maintain compatibility with older bookmarks and external links.
Redirection is typically implemented using server configurations that detect incoming requests on port 80 and forward them to port 443. This process is seamless and usually happens without the user noticing.
Firewall and Network Configuration
Firewalls and network devices are often configured with specific rules for ports 80 and 443. Since these ports are widely used, they are usually allowed by default in most network environments.
Port 443 is particularly important because it handles secure traffic. Blocking this port can prevent access to many modern websites and services.
While it is technically possible to run HTTP or HTTPS on different ports, doing so can create compatibility issues. Standard ports simplify configuration and ensure that applications work as expected across different networks.
Security Vulnerabilities in Both Ports
Although HTTPS is significantly more secure than HTTP, it is not completely free from vulnerabilities. Issues can arise due to improper configuration, outdated certificates, or weak encryption settings.
For example, an expired certificate can cause browsers to display warnings, reducing user trust. Misconfigured servers can also expose sensitive data or create opportunities for attackers.
HTTP, on the other hand, has inherent vulnerabilities due to its lack of encryption. These include data interception, content injection, and susceptibility to attacks on public networks.
Understanding these risks is essential for making informed decisions about which port and protocol to use.
Use Cases for Port 80
Despite its limitations, port 80 still has valid use cases. It is commonly used for redirection, as mentioned earlier. It is also useful in controlled environments where security risks are minimal.
For example, internal networks within organizations may use HTTP for communication between systems. Since these networks are protected by firewalls and other security measures, the risk of interception is reduced.
Developers may also use port 80 for testing purposes. Its simplicity makes it easier to set up and troubleshoot applications during development.
Use Cases for Port 443
Port 443 is the standard choice for any scenario that involves sensitive data or public access. This includes websites that handle user accounts, financial transactions, or personal information.
It is also used for secure APIs, cloud services, and communication between distributed systems. In modern applications, HTTPS is often required by default.
Even websites that do not handle sensitive data benefit from using HTTPS. It provides a secure browsing experience and helps build trust with users.
Are Port 80 and Port 443 the Same
In a broad sense, both ports serve the same purpose of enabling web communication. They allow clients and servers to exchange data and display web content.
However, the way they achieve this differs significantly. Port 80 focuses on simplicity and accessibility, while port 443 emphasizes security and trust.
A useful way to think about this is to imagine two roads leading to the same destination. One road is open and unprotected, while the other is guarded and monitored. Both will get you there, but one offers a much safer journey.
The Future of Web Communication
The internet is continuously evolving, and security has become a central focus. As threats become more advanced, the need for secure communication will only increase.This shift is closely tied to how deeply the internet is integrated into everyday life. From online banking and shopping to remote work and cloud storage, users depend on digital platforms for critical activities. Each interaction involves data exchange, and without proper security, that data can become a target for cybercriminals. This makes encryption and secure protocols essential rather than optional.
Organizations are also recognizing that security is not just a technical requirement but a business priority. A single data breach can lead to financial losses, legal consequences, and long term damage to reputation. As a result, companies are investing more in secure infrastructure, regular system updates, and continuous monitoring to protect their networks.
At the same time, governments and regulatory bodies are introducing stricter data protection laws. These regulations require businesses to implement strong security measures, including encrypted communication, to safeguard user information. Compliance is no longer just about avoiding penalties, but also about maintaining customer trust.
As technology continues to grow, secure communication will remain a cornerstone of a safe and reliable internet.
Port 443 and HTTPS are expected to remain dominant in the future. Many organizations are already moving toward enforcing HTTPS for all connections, eliminating the use of HTTP entirely.
Technologies such as secure by default protocols and automated certificate management are making it easier to implement HTTPS. This trend is likely to continue as the internet becomes more security conscious.
Practical Implications for Developers and Users
For developers, the choice between port 80 and port 443 is clear in most cases. Public facing applications should always use HTTPS to protect user data and ensure compliance with modern standards.For developers, the choice between port 80 and port 443 is clear in most cases. Public facing applications should always use HTTPS to protect user data and ensure compliance with modern standards.
Developers must also manage certificates, configure servers correctly, and monitor for potential vulnerabilities. These responsibilities are essential for maintaining a secure environment.
For users, understanding the difference between HTTP and HTTPS can help them make safer decisions online. Recognizing secure connections and avoiding insecure sites can reduce the risk of data exposure.
Conclusion
Port 80 and port 443 are both fundamental components of internet communication, but they represent different stages in the evolution of the web. Port 80, associated with HTTP, played a critical role in the early development of the internet by providing a simple and accessible way to transfer data. However, its lack of security has made it less suitable for modern applications.
Port 443, associated with HTTPS, addresses these limitations by introducing encryption, authentication, and data integrity. It has become the standard for secure communication and is widely used across all types of web applications.
While both ports serve the same basic purpose, the differences between them highlight the importance of security in today’s digital world. The shift from HTTP to HTTPS reflects a broader commitment to protecting user data and ensuring safe online interactions.
Understanding these concepts provides valuable insight into how the internet works and why secure communication is essential. As technology continues to advance, the principles behind port 443 and HTTPS will remain central to the future of networking.